GNSS spoofing has moved from a theoretical lab exercise to an operational reality. Since 2022, aviation authorities, airlines, shipping operators, and regulators have documented a sharp and sustained rise in GNSS interference across Europe, the Middle East, and parts of Asia. What began as isolated incidents around conflict zones has evolved into a persistent feature of the operating environment. In some regions, interference is now effectively continuous. The aviation sector is already treating GNSS spoofing as a frontline safety issue. The automotive industry should pay attention — because the same radio environment affecting aircraft also affects vehicles operating underneath it.
What GNSS spoofing is
In a spoofing attack, a counterfeit satellite signal is transmitted at higher power than the legitimate one. The receiver locks onto the fake signal and computes a false position, false velocity, or false time — often while reporting normal confidence levels to the application layer. Jamming overwhelms a GNSS receiver with radio noise until it loses satellite lock.
Today, commercially available software-defined radios costing only a few hundred pounds, combined with open-source GNSS simulator software, are enough to generate credible spoofing signals in controlled environments.
GNSS spoofing incidents have surged since 2022
The clearest public evidence comes from aviation, where reporting obligations make the problem visible.
In July 2024, the European Union Aviation Safety Agency (EASA) issued Revision 3 of Safety Information Bulletin 2022-02, warning of continued growth in GNSS “outages and alterations” affecting aircraft operations across the Baltic region, Black Sea, eastern Mediterranean, and Middle East. Industry groups now describe spoofing as a systemic operational threat rather than an isolated anomaly.
More than 46,000 aircraft reported satellite navigation problems over the Baltics between August 2023 and March 2024. In early 2026, the Strait of Hormuz, interference affected 1,100 ships in the first 24 hours of conflict. Vessels are also using the spoofing tactic to stay undetected in these waters.
Meanwhile, live monitoring platforms such as GPSJAM and OPSGROUP’s reporting systems show persistent daily interference zones that closely correlate with current geopolitical conflicts.
Conflict zones and the spillover problem
One of the biggest misconceptions about GNSS spoofing is that it is “contained” to military operations. It is not. A spoofer broadcasting from a military installation to mislead drones or missiles does not stop at a national border. Civilian receivers, including the GNSS module in a passenger car, can lock onto whatever strongest signal they hear.
That includes:
- passenger vehicles
- commercial fleets
- motorcycles
- agricultural equipment
- autonomous delivery systems
- robotaxis
The geography of contemporary GNSS spoofing is dominated by a handful of hotspots across the world including the Baltics, the Black Sea and the Russia-Ukraine border, and the Persian Gulf and the Strait of Hormuz. For global automotive OEMs, this matters because the primary interference hotspots overlap directly with commercially important markets.
Why GPS spoofing matters specifically to automotive OEMs
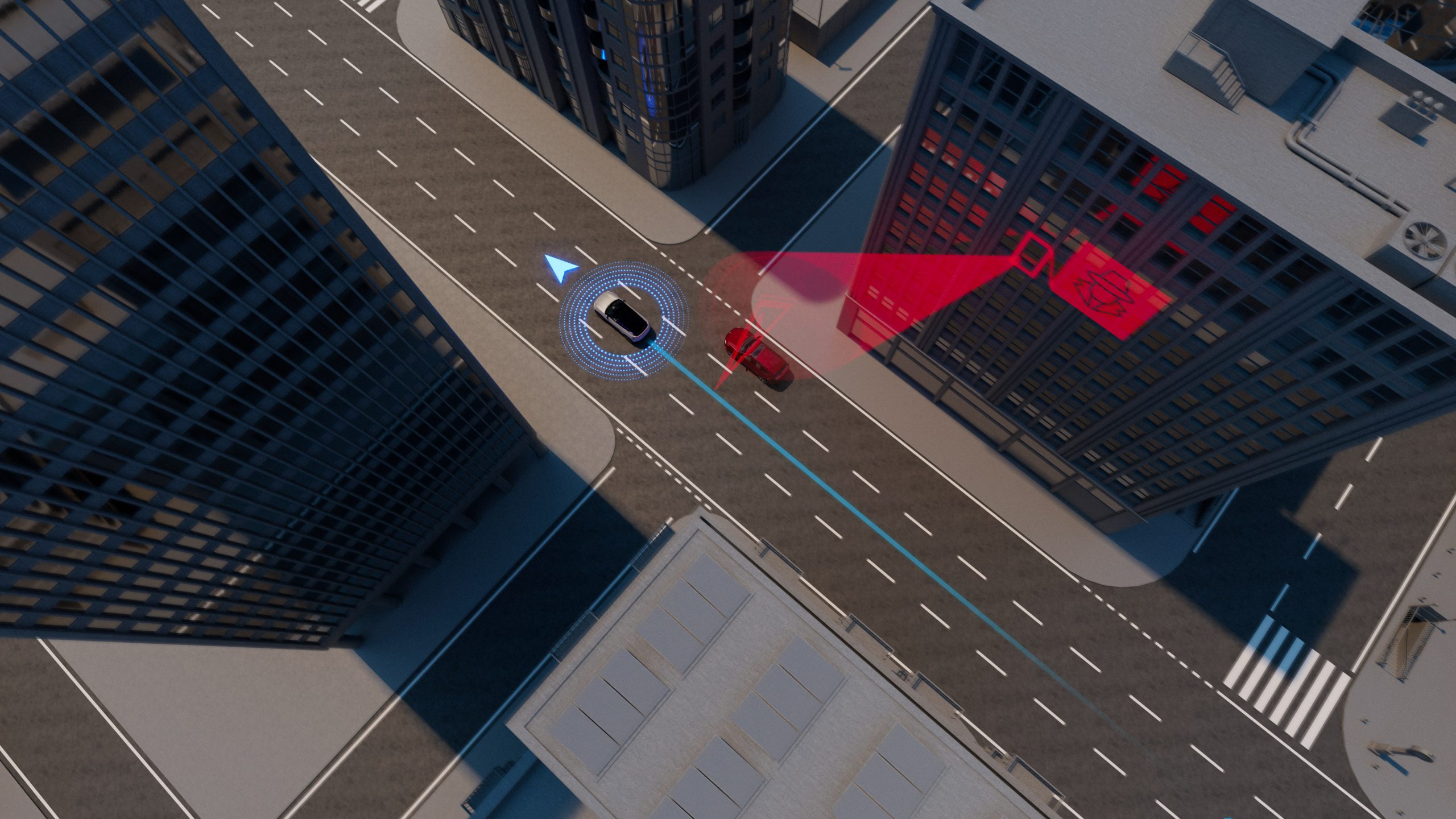
Modern ADAS and emerging Level 2+/Level 3 systems increasingly use GNSS not simply for localisation, but for behavioural context.
GNSS is used to determine which road the vehicle is on, validating map alignment, enforcing geofenced autonomy zones and enabling lane-level navigation. A spoofed fix can silently alter the operational assumptions of the vehicle. The vehicle may believe it’s on a different lane, in a different geofence, or outside a restricted zone, which may change how assistance systems behave, without an obvious warning to the driver. The implications extend beyond autonomy.
Connected services and regulatory features are positioning-dependent in ways that have legal implications. eCall in the EU transmits a location to emergency services after a crash. A spoofed location is could be a misrouted ambulance, where even being on the wrong side of the street could have serious consequences.
Regulators are increasingly treating GNSS manipulation as part of the automotive cybersecurity threat surface. UNECE Regulation No. 155 (UN R155) and ISO/SAE 21434 require OEMs to identify, assess, and mitigate cyber threats throughout the vehicle lifecycle. Positioning systems are now explicitly referenced in multiple threat-modelling frameworks and security discussions tied to vehicle type approval.
That matters because regulators are moving from “awareness” toward evidence. Increasingly, OEMs will be expected to demonstrate:
- spoofing awareness
- detection capability
- mitigation strategies
- graceful degradation behaviour
- resilient positioning architectures
An OEM that cannot demonstrate spoofing detection and mitigation will face increasingly pointed questions from regulators and approval authorities.
Supercorrelation®: GNSS spoofing resilience
FocalPoint’s Supercorrelation® technology helps protect the integrity of GNSS positioning directly within the receiver. Its software-based approach is particularly attractive to automotive OEMs because it runs on existing silicon, avoiding the need for hardware redesigns or waiting for next-generation secure chipsets to reach production vehicles.
Built as a software layer on top of conventional GNSS receivers, Supercorrelation enhances spoofing resilience while remaining compatible with today’s platforms. Results from Jammertest in Norway demonstrate how the technology can successfully defend against GNSS spoofing attacks.
FocalPoint is actively collaborating with leading chipset manufacturers to advance spoofing resilience solutions. Contact us to learn more.